Ultimate Trust (GPG Keys)
Why ultimate trust is required
Normally, GPG enforces its “web of trust” model, asking the user to confirm whether a key should be trusted before allowing encryption, signing, or verification. In a non‑interactive environment, these prompts would block execution and cause automation to fail.
Marking a key with ultimate trust tells GPG that you fully trust the key’s owner and that no additional confirmation is required when using it. This fits our needs perfectly. You should never encrypt passwords with someone else’s key, and that’s especially true if you don’t ultimately trust the key in the first place. This bypasses the trust checks and ensures that operations like encrypting backups, signing data, or verifying signatures can run unattended. Without ultimate trust, GPG may refuse to proceed or hang waiting for input, which is unacceptable in scripting and CI/CD pipelines.
For this reason, ultimate trust is a practical requirement in automation scenarios. It guarantees that your scripts can execute reliably without human intervention. Only apply ultimate trust to keys you control or explicitly trust, as it overrides GPG’s safety checks. This balance between security and usability is what makes ultimate trust essential in automated workflows.
How to setup a key as ultimately trusted
Follow these steps to configure your GPG key with ultimate trust from the terminal or command prompt, ensuring it can be used by Passwords. Untrusted keys cannot encrypt passwords.
gpg --edit-key <KEY>
gpg> trust
Your decision? 5
Do you really want to set this key to ultimate trust? (y/N) y
gpg> save
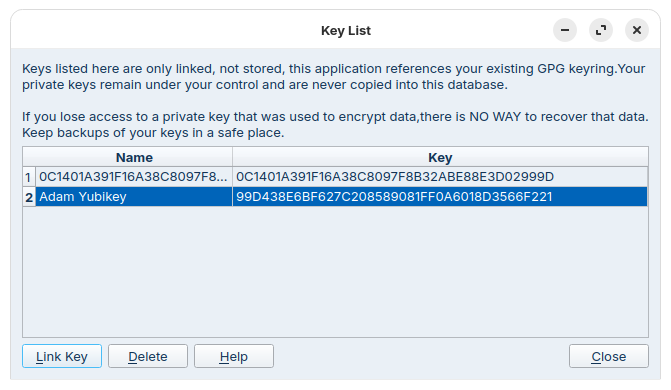
Once this step has been completed, you can re-try linking the key into Passwords.